How to Protect Your Data
Guarding your information online is dependably vital for both business and individual reasons. Doing so keeps anybody from abusing your own data for their benefits.
There are different ways of safeguarding your information on the web. One of them is having a protected association among you and your clients.
With programmers continually attempting to find potential security breaks in sites, virtual entertainment records, and programming, it’s basic to know the correct ways of safeguarding your information on the web.
This article will give you twelve procedures you can use to safeguard your information and limit the possibilities of programmers accessing your own data.
What you really want to be aware to safeguard your information on the web
Introduce Antivirus
Obviously, the main thing you want to safeguard your information online is an antivirus. It’s basically programming that can fight off a great deal of malware assaults from your PC successfully.
The extraordinary thing about having an antivirus is that you can disregard its presence, let it run behind the scenes, and consequently lead malware examining and expulsion. While your working framework gives its antivirus programming, it doesn’t offer a ton of insurance.
Going for an outsider antivirus is the better decision. Whenever you’ve picked an antivirus, you’ll have to every year recharge it. So a decent idea is set the recharging system consequently.
Consequently you get an undeniable antivirus with consistent insurance without expecting to accomplish a lot of work about it.
Make Solid Passwords
With most information breaks happening in light of feeble or taken passwords, you and your group really must areas of strength for authorize rehearses.
With a large portion of your representatives telecommuting and approaching the organization anyplace, a security break is possible higher. In this way, you want to safeguard your personality on the web.
Here are a few ways to make solid passwords:
Never reuse old passwords.
Make it longer than ten characters.
Utilize a blend of capitalized and lowercase letters, numbers, and significant characters.
Fortunately, in the event that you find making one of a kind passwords an issue, there are devices that can help. A secret phrase generator can assist with making new and secure passwords, and afterward you can store the passwords in a protected secret phrase vault.
Thus, you’ll just need to recollect one expert secret key to get to your different passwords. A portion of the notable instruments incorporate Dashlane, LastPass, and 1Password.
Be Mindful About Open Wi-Fi
Something individuals will quite often do these days is utilized free open Wi-Fi. While it is generally quick and simple to associate with, public WiFi accompanies not many safety efforts.
This implies that anybody inside a similar Wi-Fi organization can undoubtedly get to your information and take your own data easily.
Consequently, attempt just utilizing public Wi-Fi to ride the web and not web based shopping or signing into your monetary records.
Utilize a VPN
At the point when you’re associated with a public Wi-Fi organization, consistently utilize a virtual confidential organization (VPN). It encodes your web traffic and reroutes it through one of the numerous servers claimed by the VPN organization. This implies nobody can gain admittance to your information.
VPN likewise conceals your IP address, so promoters and site trackers that utilization your area to impact out advertisements will rather see the IP address of the VPN’s organization.
A decent extra eccentricity of utilizing a VPN is that you can get to content that would somehow be inaccessible in your nation of origin.
Encode Your Information
You and your clients should trade data at whatever point an exchange or activity is made. For the information to stay secure during the exchange, you can utilize a Safe Attachment Layers (SSL) convention to guarantee that the delicate data sent is safeguarded. This implies that it assists make the checkout with handling more secure.
Adding to that, starting around 2018, SSL is a priority on your site. This is on the grounds that Google Chrome and other internet browsers will stamp any site without a SSL authentication as possibly hurtful.
Fortunately, some facilitating suppliers incorporate a free SSL endorsement when you buy one of their facilitating plans. If not, you can constantly get it from autonomous suppliers like Cloudflare.
Check assuming that the Site is Secure
Prior to entering your own data on a site, ensure that it without a doubt has a SSL declaration. To find out, you can just gander at the site address in your program’s hunt bar.
Check whether there is a green latch symbol, a green bar, or HTTPS toward the start of the URL.
Alternate ways of checking whether the site is secure is to go to their protection strategy, use contact data, or see a confirmed seal from web security organizations.
Update Your Working Framework
Programmers are continuously attempting to track down defects in your framework. They’ll exploit the working framework or other programming weaknesses and addition pernicious code to enter through the security hole.
Fortunately, programming designers are generally keeping watch for security openings, and they fix them when they’re found to keep programmers from truly entering your framework. That is the reason normal working framework refreshes are significant for your site’s security.
By refreshing your working framework, the recently realized weaknesses are fixed, and programmers should begin looking all once more for potential security defects in your working framework.
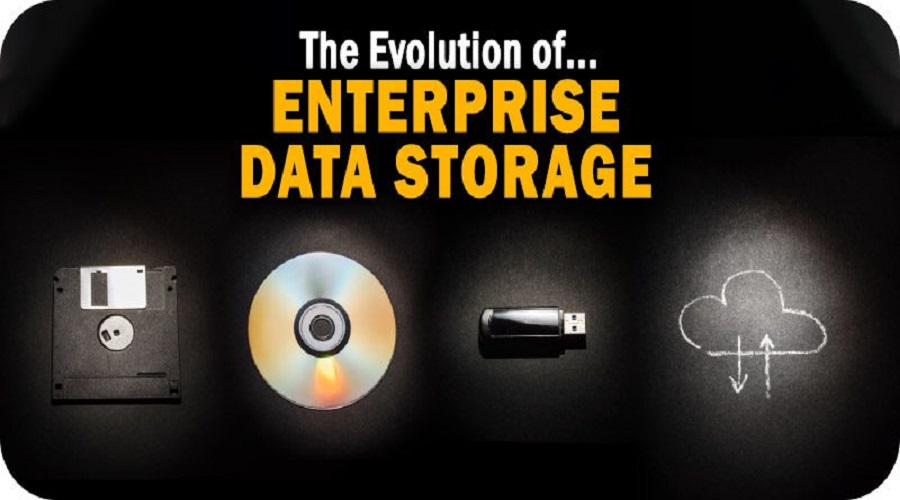
Reinforcement Your Information
This is a frequently disregarded at this point critical piece of safeguarding your site. Since regardless of how enthusiastically you attempt to guarantee your information’s security, mishaps can in any case happen.
To forestall any undesirable loss of significant information, directing normal reinforcements can keep your indispensable data secure.
However, reinforcements are additionally helpless whenever kept in similar server as your essential information. In this way while directing reinforcements, take a stab at putting away your records in a safe area, ideally the cloud arrangements.
Fortunate for you, facilitating suppliers typically remember mechanized reinforcements for their facilitating plans. Hence you don’t need to stress over routinely doing reinforcements for your site.
You just have to set the reinforcement recurrence, whether it is day to day, week by week, or month to month. Your web host will likewise give reclamation focuses to recover your reinforcements.
Keep away from Oversharing via Web-based Entertainment
A typical issue many individuals face these days is oversharing their own data on their virtual entertainment accounts. Individuals tend not to focus while posting their area, birthday, old neighborhood, and other individual data.
This is particularly pivotal in the event that you have your virtual entertainment accounts open for general society, meaning anybody on the web sees your posts.
A decent idea is to keep your online entertainment accounts hidden and just let individuals you in on view your substance. This strategy decisively diminishes the gamble of individuals abusing your own data would it be advisable for you unintentionally uncover them.
Utilize Your Cell phone For Installments
These days, you can set up your cell phone as your essential installment gadget. It begins by contributing the data about your credit/charge card that you’ll use for installment. Furthermore, that is all there is to it, the arrangement interaction is straightforward.
A great deal of retail location terminals are as of now supporting cell phone based installments. Furthermore, it’s superior to utilizing an actual card since portable installment will produce a one-time validation code that is just really great for one exchange.
This disposes of the chance of information burglary since regardless of whether they get the code, it would as of now not be legitimate.
Secure Your Remote Organizations
While a great many people are as of now acquainted with this, it’s as yet a decent suggestion to continuously get your remote organization at home or office.
Doing so keeps unapproved individuals inside your area from capturing your remote organization, regardless of whether they simply needed to get web access.
Just information a secret key or conceal your remote organization from the general population. To conceal your Wi-Fi organization, set up the Help Set Identifier (SSID) and make it undetectable to the general population.
Utilize Two-Component Validation
Two-factor verification is a viable method for further developing your site security essentially. It works by requiring two distinct login techniques to get to your information.
Normally, the main strategy is your standard secret phrase, and the subsequent technique is either a time sensitive produced code or mystery questions.
Google Authenticator is one of the most utilized two-factor validation apparatuses on the grounds that it sends time sensitive codes to your cell phone that is connected to your email and reestablishes them at regular intervals.
Consequently in a most dire outcome imaginable, where a programmer figures out how to get your login certifications and attempts to get to your information, they are impeded in light of the fact that they actually need to utilize an extra verification strategy.
Extra Ways Of safeguarding Your Own Data On the web
Make solid passwords
Don’t overshare via web-based entertainment.
Utilize free Wi-Fi with alert.
Keep an eye out for connections and connections.
Verify whether the site is secure.
End
Safeguarding your information online is a higher priority than at any other time, fundamentally as a result of the great joblessness rate around the world, making programmers be more merciless with regards to finding potential security openings in your site or virtual entertainment accounts.
In this manner, to limit and ideally keep programmers from truly gaining admittance to your information, you can Protect Your Gadgets and Organizations with these twelve stages:
Introduce an Antivirus
Make Solid Passwords
Be Wary About Open Wi-Fi
Utilize a VPN
Encode Your Information
Check assuming that the Site is Secure
Update Your Working Framework
Reinforcement Your Information
Keep away from Oversharing via Online Entertainment
Utilize Your Cell phone For Installments
Secure Your Remote Organizations
Utilize Two-Variable Confirmation
All that is passed on to do is apply these safety efforts that make it incredibly challenging for programmers to get their hands on your information.
Best of luck!